Access Control
In the A1 Security Cameras view, access control are measures taken to restrict entry to and within a given household or business. In a sense, such measures under this moniker provide homes, companies, research facilities, and more with the capacity to restrict who may be in a given specified area or the building in general. In this category, you will find multiple measures that can help you enhance your surveillance and security systems. The integration of such products have a proven effect on improving any business process or the safety of a home.
Access Control Systems Categories
Access Control Systems by Brands
What is access control systems?
Access control has different definitions depending on if it is used physically or cybernetically. In the case of A1 Security Cameras, we entirely mean physically with the products we sell focusing on the increase of physical security around doors, entrances, exits, and wherever an employee may have to show identification in one measure or another. Specifically for an employer, it provides the ability to restrict who may access what in a physical location. For example, all employees can have key cards that allow them access to the general facility, but only those at a managerial level may access rooms with business-specific information like files, money, or other valuables.
Read Ultimate Guide: What is an Access Control System?
What are the four types of access control?
In essence, security experts may use one or more official types of security for a given location. Whereas some may be as simple as implementing minor changes, others at the other end of the spectrum use more sophisticated measures. Below you will find the basic concepts surrounding those used within the surveillance and security industry.
Discretionary Access Control: In short, this type of access control is based specifically on the managing entity or owner of the company. The system works based on granting each user access, referencing every entry against a list found within the centralized hardware used to manage every scanner, card swiper, fingerprint reader, and other like devices. This system is often defined by each access point granting access to specific cards, FOBs, or other types of identification and is determined individually.
Mandatory Access Control: This type of access control is much more dependent on programming and software that grants individual access based on the administrator's preferences through a multi-tiered program. Whereas in discretionary access control, a managing entity will actively program each part of the security system for a new addition, a mandatory access control system need only be edited with an additional entry in the central programming to accept the new employee, contractor, or volunteer.
Role-Based Access Control: Similar to mandatory access control, role-based access control depends on a centralized system identifying individuals and connecting each to the broader system. However, while others are individually based, this access control system is based on the titles of each person granted access. Keycards, FOBs, and other modes of access control are then assigned to individuals based on their position within the company. While the programming is still centralized, it is much more compartmentalized and organized.
Rule-Based Access Control: Unlike the other forms of access control, rule-based access control applies restrictions based on the environment within or around the company. This may apply to whether a facility or business is accessible at a given time, what may open when an alarm is active, or if it lockdowns due to specific parameters. Furthermore, such access control can integrate surveillance and alarm systems for more advanced functionality.
What makes up an access control system?
Buttons: Having a straightforward function, buttons simply initiate a function that the hardware is hardwired explicitly. For example, many businesses use buttons to open automatic doors, start alarms, or signal to an office at a specific entrance. Furthermore, buttons in access control can be used alongside surveillance to identify staff and visitors better.
Cards and FOBS: Used by hotels, businesses, and other entities, these types of devices are widely used in access control. Used on both a broad and individual basis, these devices are essentially electronic keys that either emit a specific signal or hold specific data that matches specific devices that can scan them.
Card Readers: Coming in multiple forms, a card reader is any device designed to read a keycard or FOB. This can take the form of a scanner, a device that the card can slide through, and can come with hardware like a keypad or camera. Most often, these devices either send out a signal when interacting with a matching card or only respond to cards with distinct information previously set on them.
Door Stations: Door stations can be considered a type of traditional security camera, most often featuring two-way audio. These devices can further enhance residences when featuring buttons designed to act as a type of doorbell or get the attention of a managing entity. For larger rental properties like apartment complexes or offices, door stations may feature a keypad to call a specific address.
Video Doorbell: Video doorbells are technically a type of door station, but with the adage that they are meant to be used at an entrance and specifically hail whoever grants access. In most examples, these devices are not the conduit that activates doors or grant access but are only modes of surveillance and communication. Most video doorbells are used residentially and lesser so commercially.
What are the principles of access control?
Levels of Access: Where access is granted within a system there should be parameters surrounding each level based on value. The lowest will typically have standard protocols and limitations while the highest level of access will be held to a greater standard, can have more complex restrictions, and must adhere to more stringent policies. For example, the highest access levels can be tracked when on-site and especially when conducting actions involving sensitive material or information.
Access Limitation: In essence, only providing access for those that need it is based on role and purpose. Someone in sales does not need to be in the research and development department, meaning specific positions in particular departments should only move within them unless otherwise stated. Furthermore, those that leave a given company or are demoted should have their credentials reviewed and adjusted accordingly.
Segregation of Duty: An employee, volunteer, or those granted access should use each system for a designated purpose and nothing else. In this way, each person is granted access based on their role in a specific department and will receive punishment when veering off that assignment. Also notable, this system allows a company to run smoothly due to each individual having an individual role in a given process.
What is the role of access control in an organization?
As shown, access control helps to organize a company based on granting each individual with user-specific qualifications restricted by their position, role, or other particular information. It can allow a multiroomed complex, building, institution, or other building a system where rooms with the most valuable items are restricted to those that need to access them and no one else.
Furthermore, businesses run exceptionally well when each job is done by the right person. Access control can easily help with this by only allowing specific employees to do the job they are assigned. For places that use industrial equipment or handle valuable materials, this can be essential to production. Furthermore, places that store high value objects, documents, and more can restrict access to each.
Why do we need access control?
In a perfect world, you can trust every single person you hire to have the best intentions and help make your company the best it can be. However, statistically that is not the case with companies losing millions of dollars in stolen equipment, fraud, and more every year. Access control helps organize staff to into their positions and keeps them out of other parts of the business they do not necessarily need to be in. Furthermore, such a system allows for intern company privacy, keeping strangers or customers from accessing important information. When integrated with a security and surveillance system, access control is one of the best tools at your disposal.
A1 Security Cameras offers excellent installation services to residents and business managers of Dallas Fort Worth. Our professionals can easily implement the best security camera system that features the most cutting-edge technology meant to keep you and your employees safe. Better yet, you can make your company run more efficiently through the integration of access control by our professionals. Contact us today for more information!
-

Mobotix Mx-T26B-6N016-d 6MP Outdoor IP Door Station Camera, 1.6mm Lens, Night, Dark Gray
Brand: Mobotix
Part Number: MX-T26B-6N016-D$926.00$893.02- Compression : H.264, MJPEG, MxPEG,
- Field of View (Horizontal) : 360°Field of View
- Max. FPS and Resolution : 20fps at 3072 x 2048
- Lens Type : Fixed Lens
- Lens Size : 1.6mm Lens
- Sensor Type : CMOS
- Sensor Size : 1/1.8" Sensor
- Protection Code : IP65 IK10
- Color : Dark Gray
- Environmental : Outdoor
- Aperture : F2.0
- Access Control Type : Video Door Station
- Audio Support : Built-in Microphone Built-in Speaker
$926.00$893.02 -

Mobotix Mx-T26B-6N016 6MP Outdoor IP Door Station Camera, 1.6mm Lens, Night, White
Brand: Mobotix
Part Number: MX-T26B-6N016$926.00$893.02- Compression : H.264, MJPEG, MxPEG,
- Field of View (Horizontal) : 360°Field of View
- Max. FPS and Resolution : 20fps at 3072 x 2048
- Lens Type : Fixed Lens
- Lens Size : 1.6mm Lens
- Sensor Type : CMOS
- Sensor Size : 1/1.8" Sensor
- Protection Code : IP65 IK10
- Color : White
- Environmental : Outdoor
- Aperture : F2.0
- Access Control Type : Video Door Station
- Audio Support : Built-in Microphone Built-in Speaker
$926.00$893.02 -

Radionix IDEMIA 293678660 MorphoAccess SIGMA Lite Plus Biometric, MIFARE DESFire Card Reader with Touchscreen, IP65
Brand: Radionix
Part Number: 293678660$1,818.00$1,126.34- Protection Code : IP65 IK08
- Color : Black
- Environmental : Outdoor Indoor
- Access Control Type : Card Readers
- Screen Size : 2.8"
$1,818.00$1,126.34 -

Radionix IDEMIA 293678678 MorphoAccess SIGMA Lite Plus Biometric, Prox Card Reader with Touchscreen, IP65
Brand: Radionix
Part Number: 293678678$1,992.00$1,230.06- Protection Code : IP65 IK08
- Color : Black
- Environmental : Outdoor Indoor
- Access Control Type : Card Readers
- Screen Size : 2.8"
$1,992.00$1,230.06 -

Radionix IDEMIA 293678628 MorphoAccess SIGMA Lite Biometric, HID iClass Card Reader with LED Indicator, Embedded RFID, IP65
Brand: Radionix
Part Number: 293678628$1,752.00$1,090.80- Protection Code : IP65 IK08
- Color : Black
- Environmental : Outdoor Indoor
- Access Control Type : Card Readers
$1,752.00$1,090.80 -

Radionix IDEMIA 293678615 MorphoAccess SIGMA Lite Biometric Access Device with LED Indicator, IP65
Brand: Radionix
Part Number: 293678615$1,379.00$883.18- Protection Code : IP65 IK08
- Color : Black
- Environmental : Outdoor Indoor
- Access Control Type : Card Readers
$1,379.00$883.18 -

Radionix IDEMIA 293673665 Fingerprint and Prox Card Reader with LED Indicator, IP65
Brand: Radionix
Part Number: 293673665$1,377.00$882.04- Protection Code : IP65 IK08
- Color : Black
- Environmental : Outdoor Indoor
- Access Control Type : Card Readers
$1,377.00$882.04 -

Mobotix Mx-T26B-6N016-s 6MP Outdoor IP Door Station Camera, 1.6mm Lens, Night, Silver
Brand: Mobotix
Part Number: MX-T26B-6N016-S$926.00$893.02- Compression : H.264, MJPEG, MxPEG,
- Field of View (Horizontal) : 360°Field of View
- Max. FPS and Resolution : 20fps at 3072 x 2048
- Lens Type : Fixed Lens
- Lens Size : 1.6mm Lens
- Sensor Type : CMOS
- Sensor Size : 1/1.8" Sensor
- Protection Code : IP65 IK10
- Color : Silver
- Environmental : Outdoor
- Aperture : F2.0
- Access Control Type : Video Door Station
- Audio Support : Built-in Microphone Built-in Speaker
$926.00$893.02 -

Axis 2N 01334-001 IP Force 1 Button, HD Camera, Pictograms, Reader Ready
Brand: AXIS
Part Number: 01334-001$1,889.00$1,839.73- Compression : H.264, H.263, H.263 Plus, MJPEG, MPEG4,
- Field of View (Horizontal) : 135°Field of View
- Sensor Type : CMOS
- Sensor Size : 1/3" Sensor
- Protection Code : IK10 IP69
- Material : Aluminum
- Environmental : Outdoor
- Access Control Type : Video Intercom
- Audio Support : Built-in Microphone Built-in Speaker
$1,889.00$1,839.73 -

2N IP Style 10" Touch Display Video Intercom, WaveKey Technology and AXIS ARTPEC-7 Processor - 02407-001
Brand: AXIS
Part Number: 02407-001$4,379.00$4,184.43- Compression : H.264, MJPEG,
- Field of View (Horizontal) : 144°Field of View
- Max. FPS and Resolution : 30fps at 2560 x 1920
- Protection Code : IP65 IK08
- Access Control Type : Video Intercom
- Audio Support : Built-in Microphone Built-in Speaker
- Screen Size : 10.1"
$4,379.00$4,184.43 -

Samsung Hanwha TCIS-2 Outdoor Audio Only Intercom
Brand: Hanwha Vision
Part Number: TCIS-2$2,142.00$1,509.83- Protection Code : IP66 IK10
- Color : Black
- Material : Aluminum Steel
- Environmental : Outdoor
- Access Control Type : Audio Intercom
- Audio Support : Built-in Microphone Built-in Speaker
$2,142.00$1,509.83 -

Radionix ARD-AYBS6380 Card Reader with Keypad, MIFARE EV1, Lectus Duo 3000 EV1 Line
Brand: Radionix
Part Number: ARD-AYBS6380$311.00$222.67- Protection Code : IP65 IK08 IK10
- Color : Black
- Material : Poly-carbonate (PC)
- Environmental : Outdoor Indoor
- Access Control Type : Card Readers Card Reader with Keypad
$311.00$222.67 -
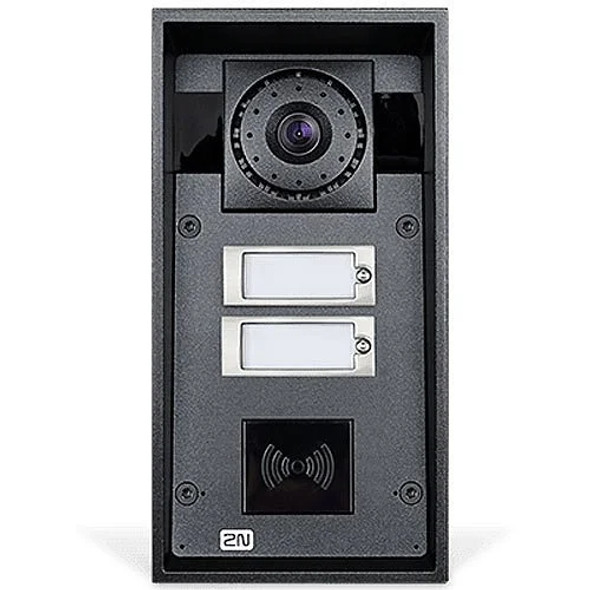
Axis 2N 01340-001 IP Force 2 Button, HD Camera, Pictograms, Reader Ready
Brand: AXIS
Part Number: 01340-001$1,849.00$1,802.18- Compression : H.263, H.263 Plus, H.264, MJPEG, MPEG4,
- Field of View (Horizontal) : 135°Field of View
- Sensor Type : CMOS
- Sensor Size : 1/3" Sensor
- Protection Code : IK10 IP69
- Material : Aluminum
- Environmental : Outdoor
- Access Control Type : Video Intercom
- Audio Support : Built-in Microphone Built-in Speaker
$1,849.00$1,802.18 -

Altronix eFlow104NA8V Access Power Controller with Power Supply/Charger - 8 Fused Relay Outputs
Brand: Altronix
Part Number: eFlow104NA8V$366.00- Color : Gray
- Environmental : Indoor
- Output Voltage : 24VDC
- Input Current : 2.7A
- Input Voltage : 220VAC
- Access Control Type : Access Power Controller
- Output Current : 9.6A
$366.00 -

Altronix eFlow104NA8DV Access Power Controller with Power Supply/Charger - 8 PTC Class 2 Relay Outputs
Brand: Altronix
Part Number: eFlow104NA8DV$366.00- Color : Gray
- Environmental : Indoor
- Output Voltage : 24VDC
- Input Current : 2.7A
- Input Voltage : 220VAC
- Access Control Type : Access Power Controller
- Output Current : 9.6A
$366.00 -

Altronix eFlow102NA8V Access Power Controller with Power Supply/Charger - 8 Fused Relay Outputs
Brand: Altronix
Part Number: eFlow102NA8V$336.60- Color : Gray
- Environmental : Indoor
- Output Voltage : 12VDC
- Input Current : 2.1A
- Input Voltage : 220VAC
- Access Control Type : Access Power Controller
- Output Current : 9.3A
$336.60 -

AXIS 2N IP Force 2.0 5MP Outdoor IP Video Intercom with 4 Buttons - 03369-001
Brand: AXIS
Part Number: 03369-001$2,259.00$2,184.34- Compression : H.264, H.265, MJPEG,
- Field of View (Horizontal) : 133°Field of View
- Lens Size : 1.935mm Lens
- Protection Code : IK10 IP69
- Material : Aluminum
$2,259.00$2,184.34 -

AXIS 2N IP Force 2.0 5MP Outdoor IP Video Intercom with 2 Buttons and Card Reader Ready - 03367-001
Brand: AXIS
Part Number: 03367-001$2,159.00$2,091.69- Compression : H.264, MJPEG, H.265,
- Field of View (Horizontal) : 133°Field of View
- Lens Size : 1.935mm Lens
- Protection Code : IP69 IK10
- Material : Aluminum
$2,159.00$2,091.69 -

AXIS 2N IP Force 2.0 5MP Outdoor IP Video Intercom with 1 Button - 03361-001
Brand: AXIS
Part Number: 03361-001$2,159.00$2,091.69- Compression : H.264, MJPEG, H.265,
- Field of View (Horizontal) : 133°Field of View
- Lens Size : 1.935mm Lens
- Protection Code : IP69 IK10
- Material : Aluminum
$2,159.00$2,091.69 -

Ubiquiti UA-G3-PRO-B Outdoor NFC Reader & Intercom with Integrated Camera, Touch Pass and PIN Access
Brand: Ubiquiti
Part Number: UA-G3-PRO-B$389.00- Field of View (Horizontal) : 98.6°Field of View
- Protection Code : IP55
- Environmental : Outdoor
- Access Control Type : Video Door Station
$389.00
